NF12 Multiple SSO Provider Support
From iDempiere en
Developer: Deepak Pansheriya Logilite Technologies
Feature Ticket: IDEMPIERE-6304
Multiple SSO Provider Support
This enhancement introduces the ability to configure and support multiple Single Sign-On (SSO) providers in iDempiere. Previously, only one SSO provider could be used at a time, and the system lacked flexibility to present multiple options at login.
With this feature, system administrators can now configure more than one SSO provider (e.g., Cognito, Keycloak) and present each as a distinct login button on the login page. This provides organizations with flexible identity provider options and improves user experience across different domains or roles.
System Configuration: SSO_SHOW_LOGINPAGE
- Y – Shows the iDempiere login page with native login and SSO provider buttons
- N – Skips the login page and redirects to SSO (if one provider) or shows only SSO buttons (if multiple)
Behavior Examples
| Providers | SSO_SHOW_LOGINPAGE | Result |
|---|---|---|
| Cognito | Y | Shows button for Cognito, allows login with iDempiere credentials |
| Cognito | N | Redirects to Cognito |
| Cognito + Keycloak | Y | Shows button for Cognito and Keycloak, allows login with iDempiere credentials |
| Cognito + Keycloak | N | Shows button for Cognito and Keycloak |
How to Configure
- Create multiple entries in the SSO Configuration window (e.g., Cognito and Keycloak).
- Set the system config:
SSO_SHOW_LOGINPAGEtoYorNdepending on your desired login experience.
- Run Cache Reset.
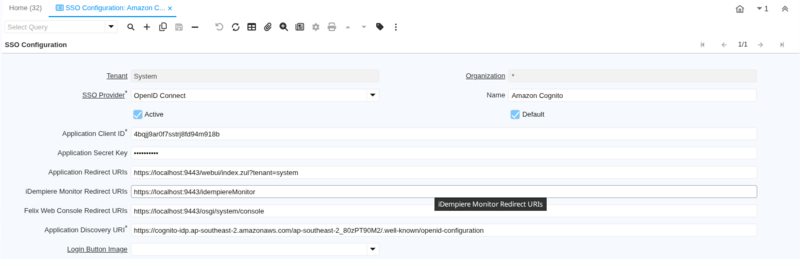
IDEMPIERE-6820 Add multi tenant support to SSO
Feature Ticket: IDEMPIERE-6304
- Change the window "SSO Configuration" to advanced and tenant level
- The selection of SSO principal configurations by tenant is via the tenant=loginPrefix query parameter.
- When the parameter is missing, it fall backs to SSO principal configurations in system tenant (i.e with AD_Client_ID=0) which should make it backward compatible.
- Uses the query parameter approach to support translation from tenant specific URL, for example from gw.idempiere.org/webui/index.zul to test.idempiere.org/webui/index.zul?tenant=gw.
- When tenant parameter exists, get SSO configuration by AD_Client_ID={AD_Client_ID of tenant parameter}.
- When no tenant parameter, get SSO configuration by AD_Client_ID=0 (effectively same as the implementation prior to this ticket).
- Tenant selection at Role selection panel is disable when tenant query parameter exists.
- SSO Configuration window changes:
- Only show configurations for current login tenant.
- The Application Client ID, Application Redirect URL and Application Discovery URI shouldn't be always updateable.
- Hide Tenant ID field if SSO Provider is OpenID Connect.
- Make Application Discovery URI and Application Client ID field mandatory if SSO Provider is OpenID Connect.
- Hide iDempiere Monitor Redirect URIs and Felix Web Console Redirect URIs field if current login tenant is not System tenant.
- Example Configurations:
- SSO Configuration for System Tenant:
- Login Prefix Setup for System tenant:
- SSO Configuration for GardenWorld Tenant:
- Login Prefix Setup for GardenWorld tenant: