Install SSL Certificate
Letsencrypt
You can use letsencrypt to generate a free certificate for your server.
The instruction to generate a certificate depends on your operating system and the http server used (or not used). Usually you can find precise instructions for your setup at https://certbot.eff.org/
This guide is about how to install the letsencrypt certificate into your iDempiere instance, instead of the self-signed certificate generated during setup.
First you need to run setup as usual. This generates a self-signed certificate in $IDEMPIERE_HOME/jettyhome/etc/keystore
After that you execute the following instructions to import the letsencrypt certificate here:
# Convert the certificate into a format Jetty can use
# execute as ROOT!!
# NOTE: the script assumes your iDempiere folder is /opt/idempiere-server, if you installed it elsewhere, then please change the path accordingly
export IDEMPIERE_HOME=/opt/idempiere-server
. $IDEMPIERE_HOME/utils/myEnvironment.sh server
# IMPORTANT!! Here you must set the variable KEYSTOREPASS with the unencrypted ADEMPIERE_KEYSTOREPASS
# default iDempiere assigns myPassword, but you could have changed it on your setup
export KEYSTOREPASS=myPassword
# NOTE: if your hostname is not the same as the registered name for letsencrypt, then set it manually here:
export DOMAIN=`hostname`
mkdir -p /tmp/key
cd /tmp/key
openssl pkcs12 -passout env:KEYSTOREPASS -export \
-in /etc/letsencrypt/live/$DOMAIN/fullchain.pem \
-inkey /etc/letsencrypt/live/$DOMAIN/privkey.pem \
-out fullchain_and_key.p12 \
-name idempiere
keytool -importkeystore -destkeystore keystore_le -srckeystore fullchain_and_key.p12 \
-alias idempiere \
-srcstorepass:env KEYSTOREPASS \
-deststorepass:env KEYSTOREPASS -noprompt
keytool -import -destkeystore keystore_le \
-file /etc/letsencrypt/live/$DOMAIN/chain.pem -alias root \
-storepass:env KEYSTOREPASS -noprompt
chown idempiere:idempiere keystore_le
cp -p keystore_le $IDEMPIERE_HOME/jettyhome/etc/keystore
rm -rf /tmp/key
Example using Comodo
During the installation of iDempiere, a self signed certificate is created and setup with tomcat server. This certificate is not authenticate with popular CA. It's common to buy a certificate from trusted CA and to replace it.
For test purpose, we use a free trial 90 day-version of comodo Free trial ssl
Step overview
Command is execute in folder [idempiere_root]/keystore
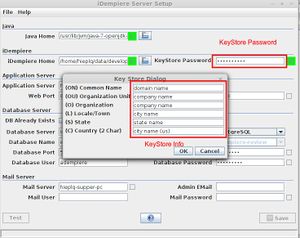
- Create KeyStore
keytool -genkey -keyalg RSA -keysize 2048 -keystore domain.keystore
this step is done during iDempiere installation.
Remember keystore password for later use
- Create CSR file (for CA as comodo make certificate for you)
keytool -certreq -keyalg RSA -file domain.csr -keystore myKeystore -alias idempiere
- Keystore file of iDempiere is myKeystore
- alias is iDempiere
- upload file domain.csr to comodo, do flow guilder of comodo
you will receive a zip file containing the files below. Extract them to [idempiere_root]/keystore: file description
- AddTrustExternalCARoot.crt (Root entity certificate)
- COMODORSAAddTrustCA.crt (Intermediate entity certificate)
- COMODORSADomainValidationSecureServerCA.crt (Intermediate entity certificate)
- domain.crt (domain entity certificate)
keytool -import -trustcacerts -alias AddTrustExternalCARoot -file AddTrustExternalCARoot.crt -keystore myKeystore keytool -import -trustcacerts -alias COMODORSAAddTrustCA -file COMODORSAAddTrustCA.crt -keystore myKeystore keytool -import -trustcacerts -alias COMODORSADomainValidationSecureServerCA -file COMODORSADomainValidationSecureServerCA.crt -keystore myKeystore keytool -import -trustcacerts -alias COMODORSADomainValidationSecureServerCA -file COMODORSADomainValidationSecureServerCA.crt -keystore myKeystore keytool -import -trustcacerts -alias idempiere -file domain.crt -keystore myKeystore
Note: use correct alias value
- Config jetty
file: %IDEMPIERE_HOME%\jettyhome\etc\jetty-ssl-context.xml Line 8: replace "etc/keystore" to "etc/myKeystore" , save.
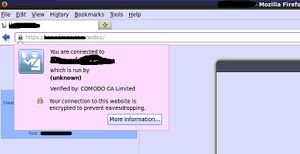
- what next?
restart iDempiere and open it in your browser.